“We’ve just traced the attack... its coming from inside the house!” How do you secure your network when the bad guys already have control of your servers? It’s so hard to keep up with the attacks, maybe it’s safer to architect with the assumption that you’ve already been breached. What does this entail?
Monday, January 13, 2020
F5 Labs: CISOs Share Their Wisdom, Advice, and Strategies
CISOs Share Their Wisdom, Advice, and Strategies
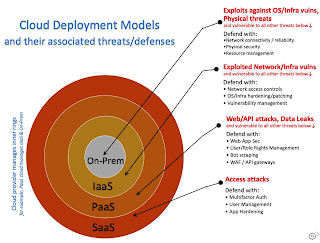
F5 Labs: Is the Cloud Safe? Part 3: How to Make it Safe
Is the Cloud Safe? Part 3: How to Make it Safe
https://www.f5.com/labs/articles/threat-intelligence/is-the-cloud-safe--part-3--how-to-make-it-safe
F5 Labs: Is the Cloud Safe? Part 2: Breach Highlights for the Past 3 Years
Is the Cloud Safe? Part 2: Breach Highlights for the Past 3 Years
F5 Labs: Is the Cloud Safe? Part 1: Models and Misadventures
Is the Cloud Safe? Part 1: Models and Misadventures
https://www.f5.com/labs/articles/threat-intelligence/is-the-cloud-safe--part-1--models-and-misadventures
Subscribe to:
Comments (Atom)